Imagine waking up to find your most valuable digital art or a rare collectible gone from your wallet in a split second. In the world of blockchain, there are no "forgot password" buttons for your private keys and no bank managers to call for a chargeback. With the NFT market hitting roughly $14 billion, scammers have scaled their operations, with fraud attempts jumping 45% year-over-year. If you're treating your NFT wallet like a casual social media account, you're essentially leaving your front door unlocked in a neighborhood where thieves have master keys. To keep your assets safe, you need a defense strategy that goes beyond a strong password.
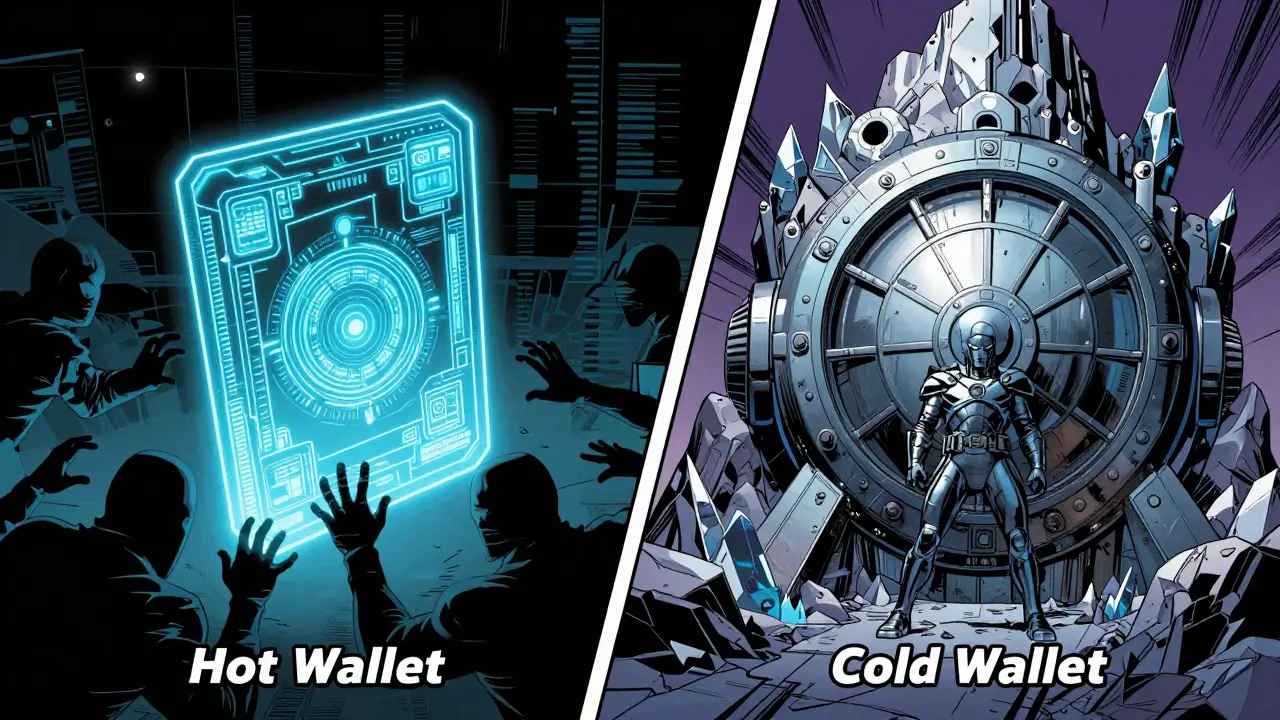
The Foundation: Cold Storage vs. Hot Wallets
The biggest mistake most collectors make is keeping all their assets in a browser extension. This is what we call a "hot wallet." While MetaMask is an incredibly convenient software wallet that allows users to interact with the Ethereum blockchain, it is inherently more vulnerable because it's connected to the internet. Data shows that nearly 19% of thefts involve these extension wallets, whereas properly used cold storage sees almost zero incidents.
For any holding worth more than $5,000, you should move your assets to a hardware wallet. Devices like the Ledger Nano X a physical security device that stores private keys offline to prevent unauthorized access or the Trezor Model T a hardware wallet designed for secure storage and transaction signing act as a physical vault. By keeping your private keys isolated from the web, you reduce your risk of remote attacks by a staggering 98%. Think of your hot wallet as a physical wallet you carry for daily spending and your hardware wallet as a high-security safe at home.
| Feature | Hot Wallets (e.g., MetaMask) | Hardware Wallets (e.g., Ledger) |
|---|---|---|
| Connectivity | Always online | Offline (Cold Storage) |
| Risk Level | Higher (vulnerable to malware) | Very Low (isolated keys) |
| Best Use Case | Small trades, minting | Long-term holding, high-value NFTs |
| Theft Incident Rate | ~18.7% (according to 2025 data) | ~0.02% |
Stopping the "Silent Drain": Managing Token Approvals
Most people think a hack happens when someone "gets into" their wallet. In reality, most NFT thefts occur because of dormant permissions. When you list an NFT on a marketplace, you often sign a transaction that gives the platform permission to move your tokens. If you give "unlimited approval" to a malicious contract, a hacker doesn't need your password; they just use the permission you already granted to drain your wallet.
This is where Etherscan a leading block explorer and analytics platform for the Ethereum blockchain becomes your best tool. Their Token Approval Checker allows you to see exactly which contracts have access to your funds. Many experienced traders find they have over a dozen active permissions they don't even remember. By regularly revoking these unused approvals, you close the backdoors that hackers love to use. If a project asks for an unlimited allowance rather than a specific quantity, consider it a massive red flag.

Navigating Marketplaces and Smart Contract Risks
Not all platforms are created equal. High-traffic sites like OpenSea the world's first and largest marketplace for buying, selling, and managing NFTs have implemented tools like EIP-712 typed data signing to stop signature spoofing. However, the burden of verification still falls on you. A common trap is the "copycat collection." You might see a project with a blue checkmark, but is it the *real* one? Verified collections typically have 94% fewer counterfeits, but scammers are getting better at mimicking the look of official pages.
Before you buy or mint, check the smart contract. Legitimate projects almost always undergo third-party audits by firms like OpenZeppelin a security-focused company that provides audited smart contract libraries and security audits. If a project's contract is unverified on a block explorer, there is a high chance it's a scam. Around 78% of fraudulent projects avoid verification because it would reveal the malicious code used to steal funds.
The "Skepticism Filter": Defeating Phishing and Social Engineering
Phishing has evolved. It's no longer just about a fake email; it's now deepfake videos and urgent Discord messages. The most common tactic is the "emergency migration" or a "surprise airdrop." They create a sense of panic with countdown timers to force you to click a link without thinking. This is why the "Five-Minute Rule" is essential: never act on a "limited time" offer immediately. Instead, verify the news through three independent, official channels (e.g., the project's official Twitter, their official Discord announcement channel, and a trusted community member).
Be especially wary of direct messages. A huge percentage of thefts in recent years started with a fake DM on Discord. If a "support agent" messages you first, they are lying. Official support teams will almost never slide into your DMs to ask for your seed phrase or to help you "synchronize" your wallet. If someone asks for your 24-word seed phrase, they are attempting to steal everything you own. Period.
A Practical Security Checklist for Collectors
Setting up a truly secure environment takes a few hours, but it saves you from a lifetime of regret. Follow these steps to harden your setup:
- Secure Your Seeds: Never store your recovery phrase in a cloud document, email, or as a photo on your phone. Use a physical metal backup that can withstand fire and water.
- Upgrade Your 2FA: Stop using SMS-based two-factor authentication, which is vulnerable to SIM-swapping. Switch to authenticator apps like Authy a multi-platform two-factor authentication app used for securing online accounts.
- Simulate Transactions: Use the "Preview Transaction" feature on marketplaces. If the simulation shows your NFT leaving your wallet but nothing entering it, do not sign the transaction.
- Network Hardening: Ensure your home Wi-Fi uses WPA3 encryption. Use privacy extensions like Privacy Badger to block scripts that could lead to session hijacking.
- Segment Your Assets: Use different accounts on your hardware wallet for different categories. Keep your "minting" account (which interacts with risky new projects) separate from your "vault" account where your most expensive art lives.
What is the difference between a hot wallet and a cold wallet?
A hot wallet is connected to the internet (like a browser extension), making it convenient for frequent trading but vulnerable to online hacks. A cold wallet is a physical device that keeps your private keys offline, meaning a hacker cannot access your funds unless they have the physical device and your PIN.
How can I tell if an NFT project is a scam?
Look for three red flags: unverified smart contracts on Etherscan, a lack of a third-party security audit (from firms like OpenZeppelin), and a heavy reliance on "urgency" or "fear of missing out" (FOMO) in their marketing. If the team is anonymous and the contract is closed, be extremely cautious.
Why do I need to revoke token approvals?
When you grant a marketplace permission to move an NFT, that permission often stays active forever. If that marketplace or the smart contract it uses is ever compromised, the attacker can use those old permissions to steal your assets without needing your password.
Is a blue checkmark on OpenSea enough to trust a collection?
No. While verification reduces the number of counterfeits, it's not a guarantee of security. Always cross-reference the collection's contract address with the project's official social media channels before making a purchase.
What should I do if I think I've been phished?
Immediately move any remaining assets to a brand new wallet with a new seed phrase. Use a tool like Etherscan's Approval Checker to revoke all permissions. Change the passwords and 2FA on all linked accounts (email, Discord, Twitter) immediately.
Next Steps for Every Level of Collector
If you're just starting out, your priority is education. Spend a few hours learning the difference between a seed phrase and a private key. If you're a mid-level collector with a few thousand dollars in assets, it's time to buy a hardware wallet and move your primary holdings off the web.
For the "whales" or pro traders, the focus should be on rigorous permission management and network security. Set a monthly calendar reminder to audit your token approvals and rotate your passwords. As AI-driven threats like deepfake verification become more common, remember that the only real security is a healthy dose of skepticism. If an opportunity looks too good to be true, it almost certainly is.

Jimmy vasquez
April 29, 2026 AT 17:50I've seen so many people lose everything because they didn't use a hardware wallet. It's the only way to sleep peacefully at night when you're holding high-value assets. If you're still on a browser extension, you're basically gambling with your security.
Robert Smith
May 1, 2026 AT 02:37Ledger is the way 🚀🔥
Emily A
May 2, 2026 AT 07:38The distinction between a private key and a seed phrase is fundamental, yet surprisingly many users conflate the two. It is imperative to understand that the seed phrase is the master key to your entire wallet architecture, whereas a private key typically governs a single address within that hierarchy. Failing to grasp this basic cryptographic principle is exactly why so many people fall prey to the same rudimentary phishing schemes over and over again. Precision in terminology leads to precision in security.
Michael Repak
May 2, 2026 AT 20:48Totally agree with the hardware wallet advice!!! It really is a game changer for peace of mind!!! Everyone should do this right now!!!
debra hoskins
May 3, 2026 AT 09:17The obsession with these plastic trinkets is a bit quaint. A truly seasoned operator knows that the real vulnerability isn't the hardware, but the hubris of the user thinking they're untouchable once they buy a Ledger. It's a facade of security for the masses.
Ryan Nakielny
May 5, 2026 AT 01:00Right, because nothing says "I'm a pro" like buying a USB stick and thinking you've solved every problem in the blockchain. Classic.
Bevon Findley
May 5, 2026 AT 18:15Standard stuff. 💅 Just use a multisig if you're actually wealthy. 😎
Nitin Gupta
May 7, 2026 AT 07:45I would like to add that using a dedicated email address just for your crypto accounts can provide an extra layer of security. It helps in keeping your financial life separate from your social and professional accounts, making it harder for hackers to find a common thread.
edie rosa
May 9, 2026 AT 03:10Typical. We talk about security but ignore the moral decay of the NFT market itself. Why protect digital pixels that add zero value to the world? It's just a circle of greed and vanity where people pretend to be tech-savvy while they're actually just gambling on JPEGs. The real security breach here is the lack of a moral compass in this entire industry.
Kristi Swartz
May 10, 2026 AT 18:47you must use a metal backup for seed phrases because paper burns and ink fades it is the only logical choice
Harvey Alford
May 11, 2026 AT 02:57Seen your wallet? Show me the assets.
Andrew Todd
May 11, 2026 AT 10:44Only losers get hacked. If you're not smart enough to see a fake link, you don't deserve to have money. Simple as that. USA leads the tech world for a reason, maybe learn from the best.
VIVEK SINGH
May 11, 2026 AT 17:19Oh look, another guide telling us not to trust strangers on the internet. Groundbreaking. Truly a philosophical leap forward in human intelligence. Maybe next we can learn that fire is hot and water is wet? How revolutionary.
AP Fisher
May 11, 2026 AT 22:51Wait, so I really need to check Etherscan for these approvals? I didn't know that was a thing. Is it free to use?
Lloyd I
May 13, 2026 AT 17:04Absolutely! Etherscan is a fantastic tool for everyone to use. It's totally free and helps you keep a clean slate with your permissions. Keep learning and staying safe, everyone!
Janis Naglis
May 13, 2026 AT 17:40This is such a great primer!!! The emphasis on the Five-Minute Rule is absolutely critical for mitigating the impact of high-pressure social engineering attacks!!! It really helps to decouple the emotional urgency from the technical execution of the transaction!!! Keep pushing for this level of diligence!!!
Tracy McBurney
May 14, 2026 AT 12:54The data regarding the 45% jump in fraud is interesting, but the author fails to mention the specific vectors of these attacks. Are we talking about smart contract exploits or simple phishing? Without a granular breakdown of the attack surface, this advice is merely anecdotal and lacks rigorous analytical depth.
Sri Astuti
May 16, 2026 AT 06:32I honestly think the whole concept of "security" in crypto is a joke because the moment you interact with a new dApp you're essentially handing over the keys to your kingdom anyway 🙄 and it's just so exhausting to keep track of a hundred different revocations every single week just to feel a tiny bit safer in a sea of sharks who are just waiting for one mistake
It's honestly a nightmare for the average user who just wants to enjoy their art without needing a degree in computer science just to not get drained by a random Discord bot!
Elle Kharitou
May 16, 2026 AT 08:08It's quite beautiful when you think about the philosophy of trust in a trustless system, isn't it? 🌟 We spend all this time building digital walls to protect our treasures, yet the greatest vulnerability is always the human heart and its desire for quick gains. We must learn to breathe through the FOMO and find a balance between the excitement of the new and the wisdom of the old. Let us be mentors to the newcomers, guiding them with kindness and patience as they navigate this wild frontier of digital ownership. 🌈✨
Lynne Teperman
May 16, 2026 AT 18:24weaving a tapestry of safety in this digital wild west is a fine art indeed... just a whisper of a reminder to keep those seed phrases far from any glowing screen
Alex Mazonowicz
May 17, 2026 AT 14:29Awesome tips!!! Really helps to see it all in one list!!! Thank you for sharing!!!
Felix Eduardo Velasquez
May 18, 2026 AT 20:49For those wondering about the "simulation" part, there are several tools like Tenderly that allow you to see exactly what a transaction will do before you sign it. It transforms the process from a blind leap of faith into a calculated move. If the state change shows a balance of zero for your asset, that's your signal to abort. It's the digital equivalent of checking the lock on a door before you walk away.